In digital forensics and legal investigations, forensic image authentication is a crucial method for identifying tampered images and videos. Digital image and video analysis is the process of looking for any indications of manipulation or alteration. In this blog today, we will investigate a few tips and tricks for forensic image authentication in image and video analysis.
Top Tips and Tricks For Forensic Image Authentication to Consider
Understand the types of image manipulation
Understanding the various types of image manipulation is essential before you begin analyzing images and videos for forensic purposes. Changing an image’s content, metadata, or file structure are all examples of image manipulation. It can likewise include replicating, gluing, or eliminating explicit components from a picture. You can identify any of these signs of tampering or alteration by understanding the various forms of manipulation.
Verify the authenticity of the source
When analyzing digital images and videos for forensic purposes, it is essential to verify the authenticity of the source. It includes analyzing the original source of the image or video to guarantee that it has not been messed with or adjusted in any capacity. Verifying the model of the camera, the time and date of the capture, and any other relevant metadata are all examples of this.
Check for inconsistencies
One important part of forensic image authentication is checking for inconsistencies. It involves looking at the image or video to see if the content, metadata, or file structure are inconsistent. For instance, assuming an image has been messed with, there might be contrasts in the color, lighting, or resolution of the image. The time and date of the capture, for example, may also differ in the metadata.
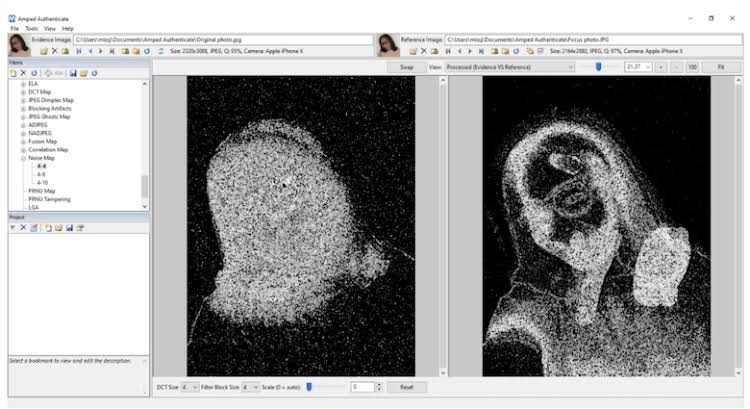
Utilize specialized software
Forensic image authentication necessitates the use of specialized software. There are a few programming devices accessible that can assist you analyze digital images and videos for signs of tampering or manipulation. You can use these tools to find artifacts, inconsistencies, and hidden information that may not be obvious to the naked eye.
Analyze the metadata
For forensic image authentication, it is essential to examine the metadata of an image or video. The metadata can contain data about the camera model, the time and date of the capture, and the area of the picture. You can spot any discrepancies that might point to tampering or manipulation by looking at the metadata.
Compare with known sources
Contrasting the picture or video with other sources can assist you with recognizing any indications of altering or control. For instance, if an image is claimed to have been taken at a specific location and time, you can check for inconsistencies by comparing it to other images taken at the same location and time.
Wrap Up
Forensic image authentication is a basic method for digital forensics and legal investigations. You can identify any signs of tampering or alteration in digital images and videos by comprehending the various forms of image manipulation, confirming the authenticity of the source, looking for inconsistencies, utilizing specialized software, analyzing the metadata, and comparing with known sources.
Note that, you can improve your forensic image authentication skills and guarantee the accuracy and dependability of your forensic analysis with the help of these tricks and tips.
